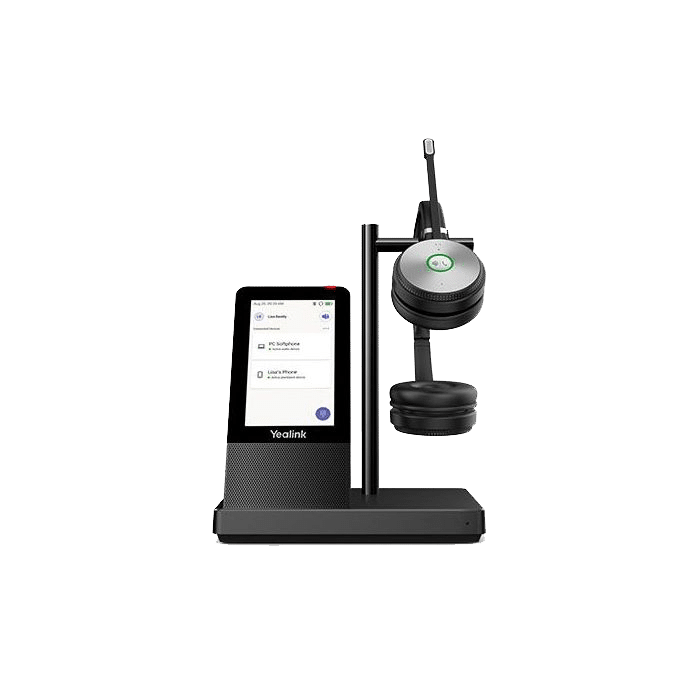
Your business’ IT requirements form a complex network that you need to all work together. From ecosystem ideation, to supply and setup; whether it’s your hardware and software working together, to a complete cloud solution. And, depending on the nature of your business, there are often regulatory standards—on both a national and industry-specific level—that your IT infrastructure needs to meet.
You can’t trust your business’ IT to just any company. You need a partner that you can rely on.